So do you realize this, lets say you go to a web site, xyz.com, but you don't worry because you have the ISP router with "virus protection" so your all set, right?? Ha Ha. If that web site is secure, like most are today, then from the browser to the web site are encrypted (that little lock symbol) and guess what, your router CAN'T SEE ANY OF THAT DATA. So you better hope that none of xyz.com advertisers, or xyz.com itself is not infected, because guess what, you are now infected.
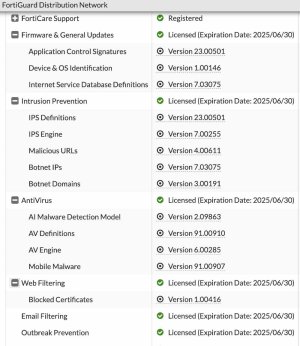
On a Fortigate, you install a certificate from the router on all your computers, or important devices, at least, and the Fortigate decrypts the encryption, scans it, that reencrypts the data so your browser puts on the lock, and everything is encrypted end-to-end, but it is also fully scanned. Regular routers don't do that. Same with encrypted DNS traffic (TLS over port 853 is better encryption than DNS over HTTPS, by the way.). And the Fortigate intercepts the DNS traffic, even if it doesn't use the DNS server you gave it. (Many use 8.8.8.8 no matter what you TOLD it to use.) And a good bit of traffic NEVER goes to a DNS server at all. The IP address is hard coded in it. If the Fortigate can't decrypt it for whatever reason, its blocked.
You can check any web address here, and they have millions. Don't forget to check your not a robot.
https://www.fortiguard.com/webfilter